Data security and encryption in Azure Data Manager for Energy
This article provides an overview of security features in Azure Data Manager for Energy. It covers the major areas of encryption at rest, encryption in transit, TLS, https, microsoft-managed keys, and customer managed key.
Encrypt data at rest
Azure Data Manager for Energy uses several storage resources for storing metadata, user data, in-memory data etc. The platform uses service-side encryption to automatically encrypt all the data when it is persisted to the cloud. Data encryption at rest protects your data to help you to meet your organizational security and compliance commitments. All data in Azure Data Manager for Energy is encrypted with Microsoft-managed keys by default. In addition to Microsoft-managed key, you can use your own encryption key to protect the data in Azure Data Manager for Energy. When you specify a customer-managed key, that key is used to protect and control access to the Microsoft-managed key that encrypts your data.
Encrypt data in transit
Azure Data Manager for Energy supports Transport Layer Security (TLS 1.2) protocol to protect data when it’s traveling between the cloud services and customers. TLS provides strong authentication, message privacy, and integrity (enabling detection of message tampering, interception, and forgery), interoperability, and algorithm flexibility.
In addition to TLS, when you interact with Azure Data Manager for Energy, all transactions take place over HTTPS.
Set up Customer Managed Keys (CMK) for Azure Data Manager for Energy instance
Important
You cannot edit CMK settings once the Azure Data Manager for Energy instance is created.
Prerequisites
Step 1: Configure the key vault
You can use a new or existing key vault to store customer-managed keys. To learn more about Azure Key Vault, see Azure Key Vault Overview and What is Azure Key Vault?
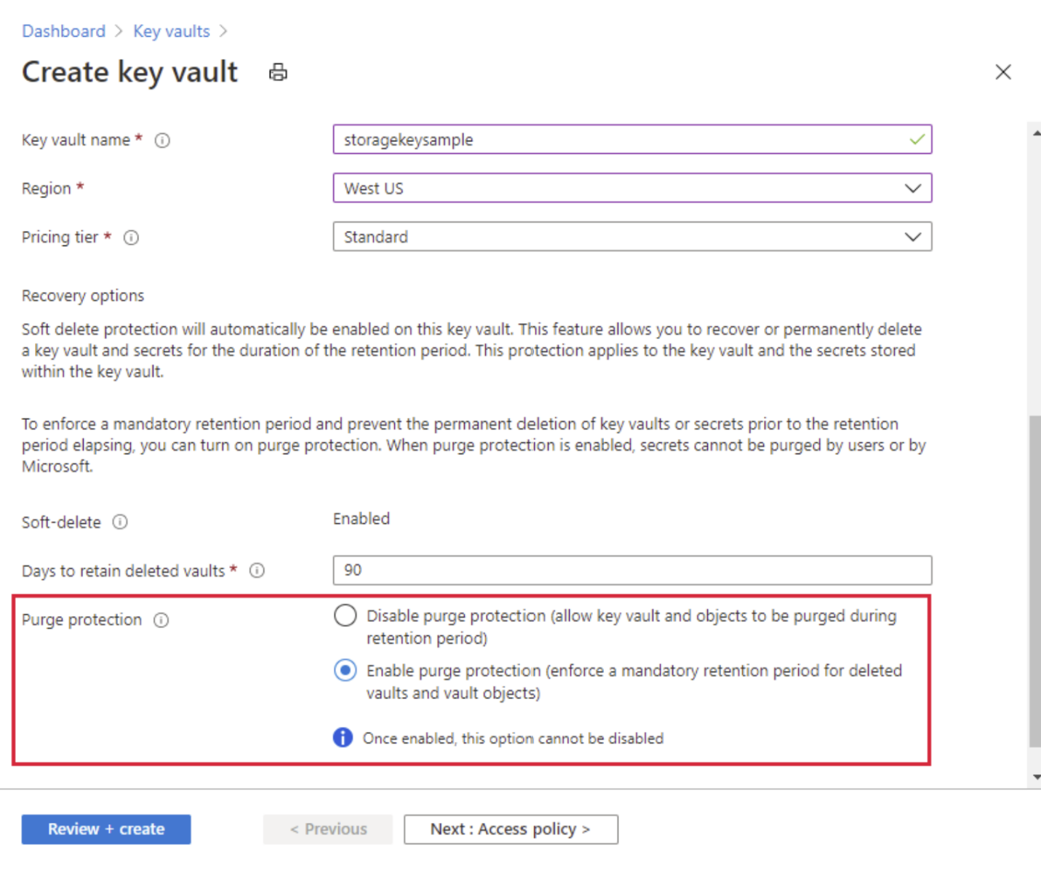
Using customer-managed keys with Azure Data Manager for Energy requires that both soft delete and purge protection be enabled for the key vault. Soft delete is enabled by default when you create a new key vault and cannot be disabled. You can enable purge protection either when you create the key vault or after it is created.
To learn how to create a key vault with the Azure portal, see Quickstart: Create a key vault using the Azure portal. When you create the key vault, select Enable purge protection.
To enable purge protection on an existing key vault, follow these steps:
- Navigate to your key vault in the Azure portal.
- Under Settings, choose Properties.
- In the purge protection section, choose Enable purge protection.
Step 2: Add a key
- Next, add a key to the key vault.
- To learn how to add a key with the Azure portal, see Quickstart: Set and retrieve a key from Azure Key Vault using the Azure portal.
- It is recommended that the RSA key size is 3072, see Configure customer-managed keys for your Azure Cosmos DB account | Microsoft Learn.
Step 3: Choose a managed identity to authorize access to the key vault
- When you enable customer-managed keys for an existing Azure Data Manager for Energy instance you must specify a managed identity that will be used to authorize access to the key vault that contains the key. The managed identity must have permissions to access the key in the key vault.
- You can create a user-assigned managed identity.
Configure customer-managed keys for an existing account
- Create a Azure Data Manager for Energy instance.
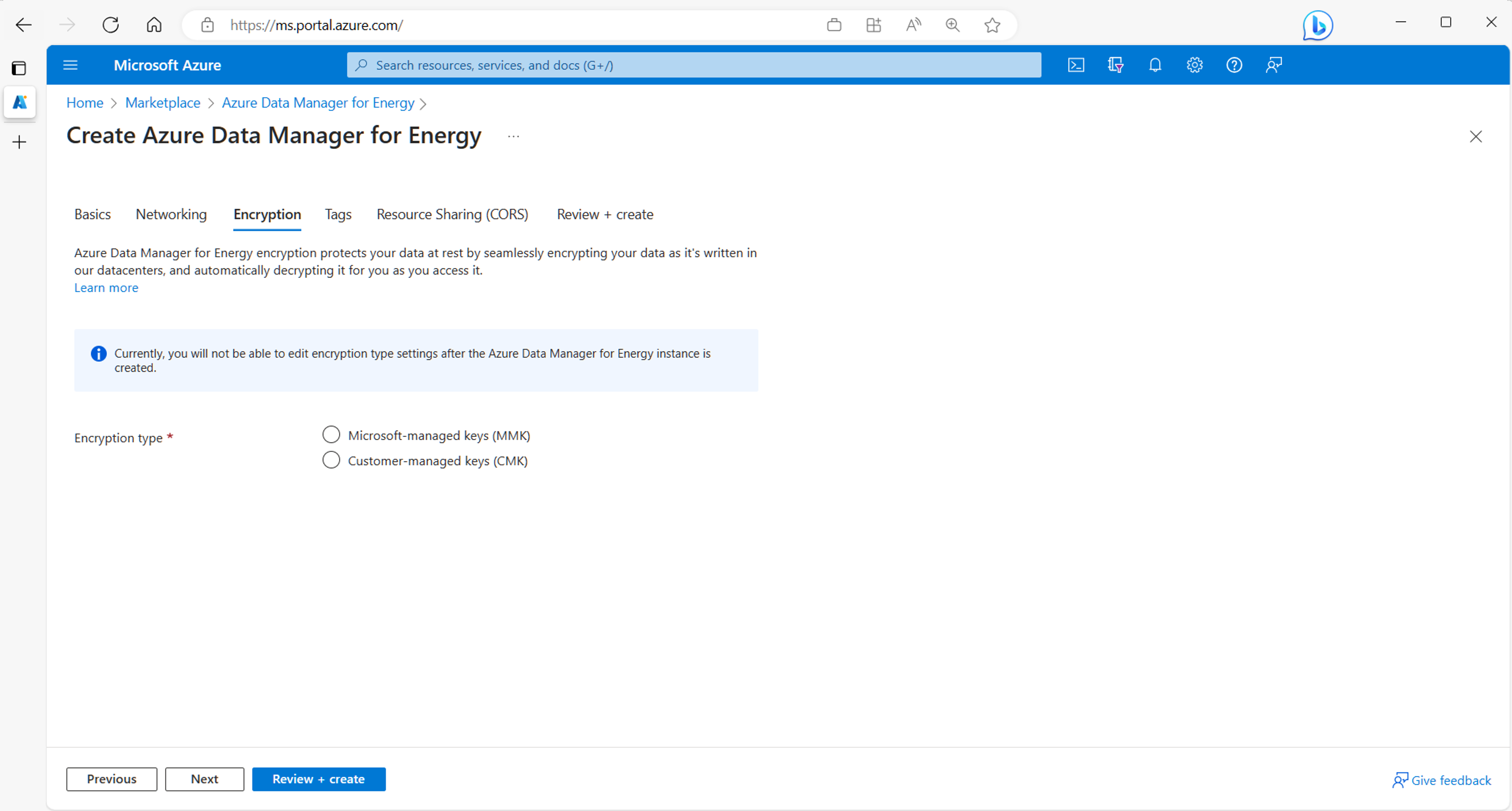
- Select the Encryption tab.
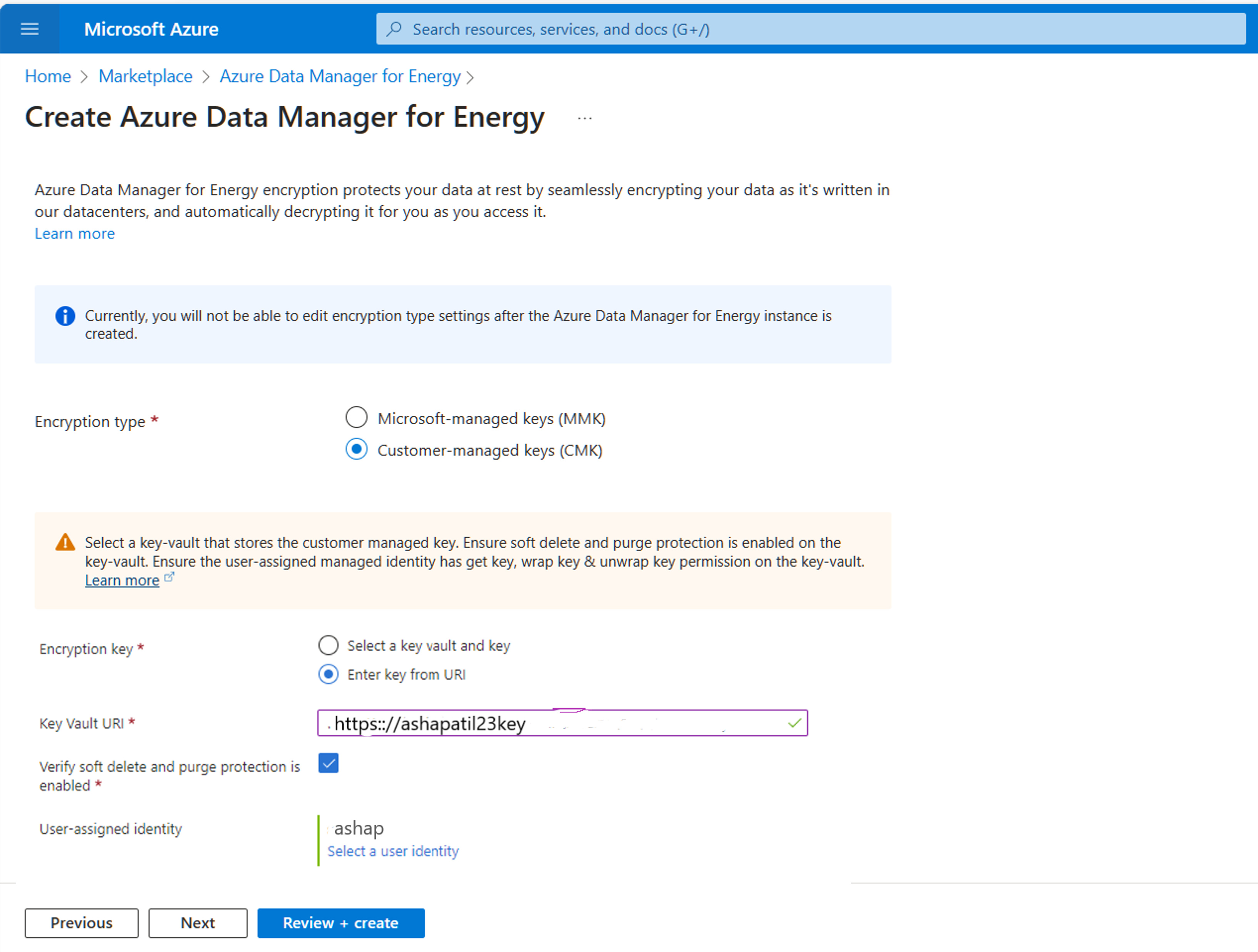
In the encryption tab, select Customer-managed keys (CMK).
For using CMK, you need to select the key vault where the key is stored.
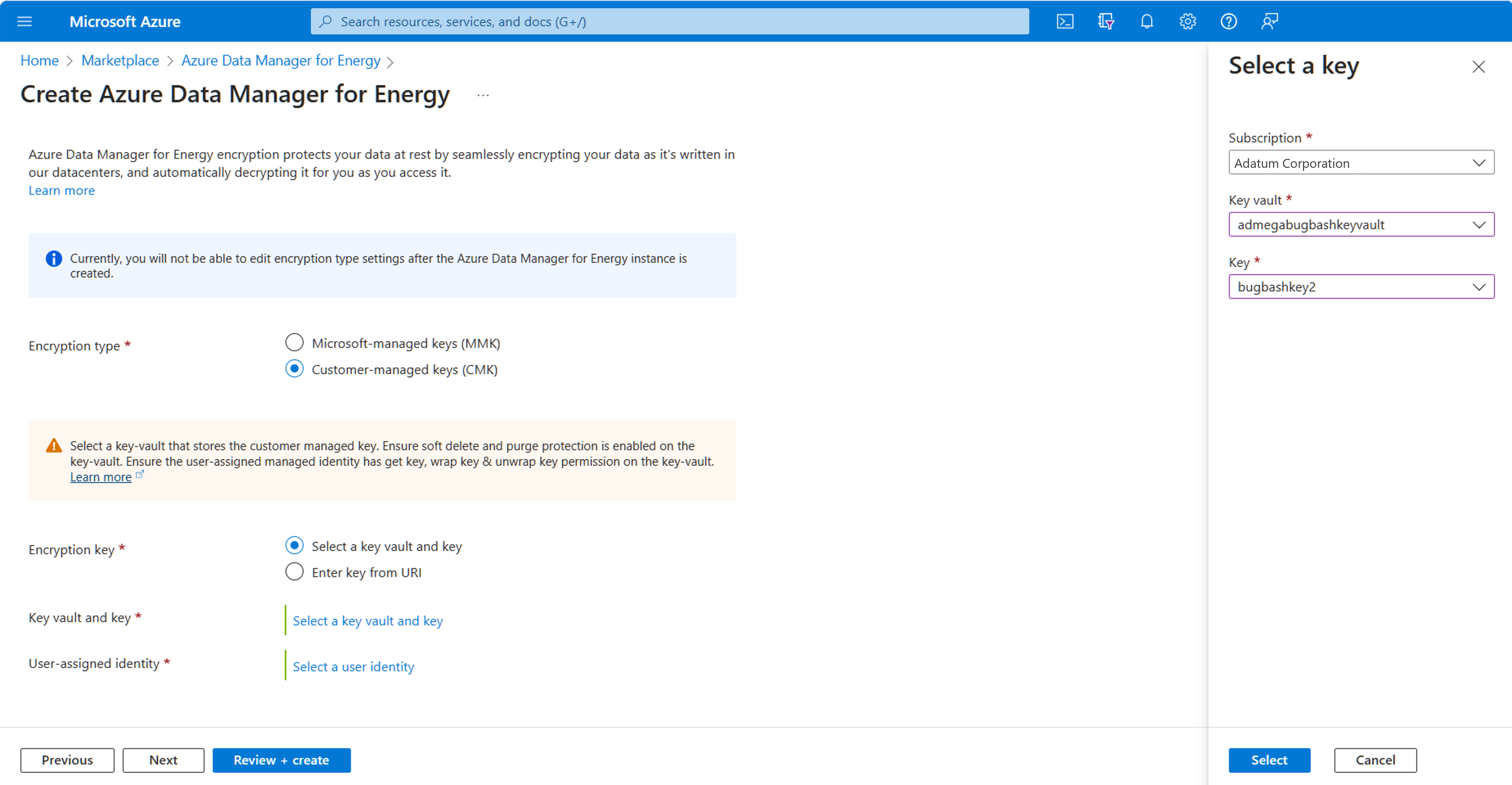
Select Encryption key as “Select a key vault and key.”
Then, select “Select a key vault and key.”
Next, select the key vault and key.
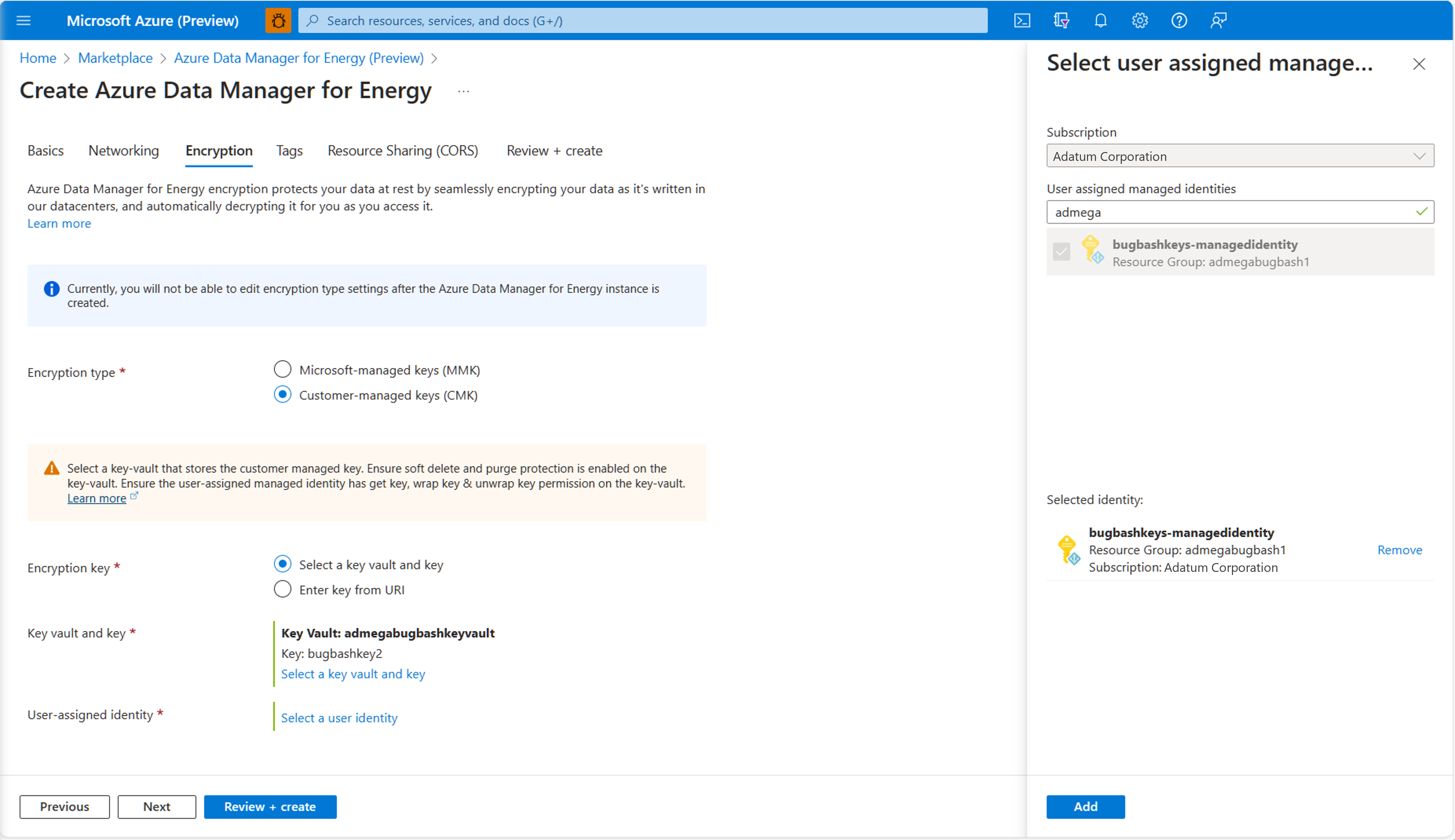
Next, select the user-assigned managed identity that will be used to authorize access to the key vault that contains the key.
Select “Select a user identity.” Select the user-assigned managed identity that you created in the pre-requisites.
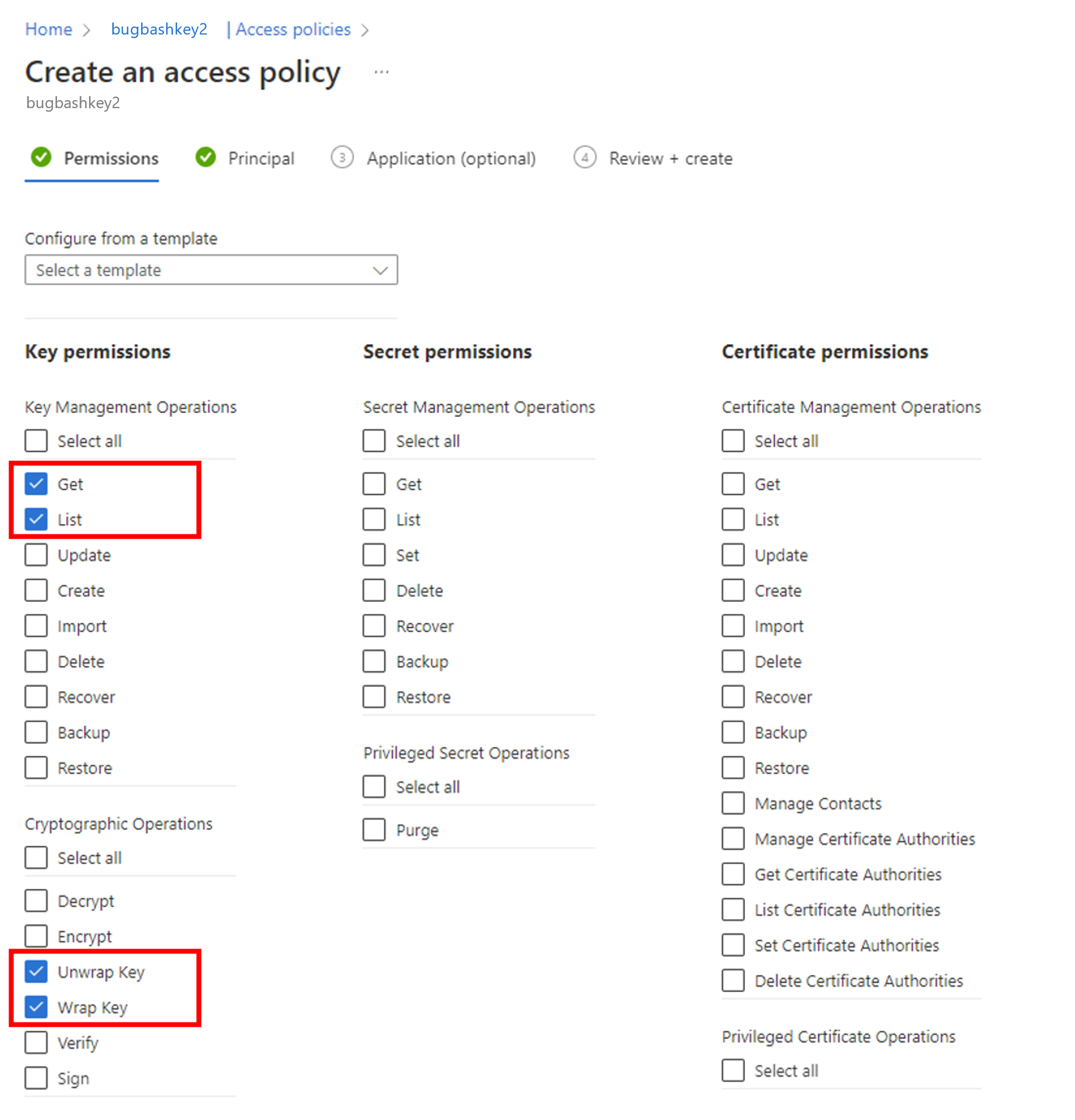
This user assigned identity must have get key, list key, wrap key, and unwrap key permissions on the key vault. For more information on assigning Azure Key Vault access policies, see Assign a Key Vault Access Policy.
You can also select Encryption Key as “Enter key from Uri.” It is mandatory for the Key to have soft delete and purge protection to be enabled. You will have to confirm that by checking the box shown below.
Next, select “Review+Create” after completing other tabs.
Select the "Create" button.
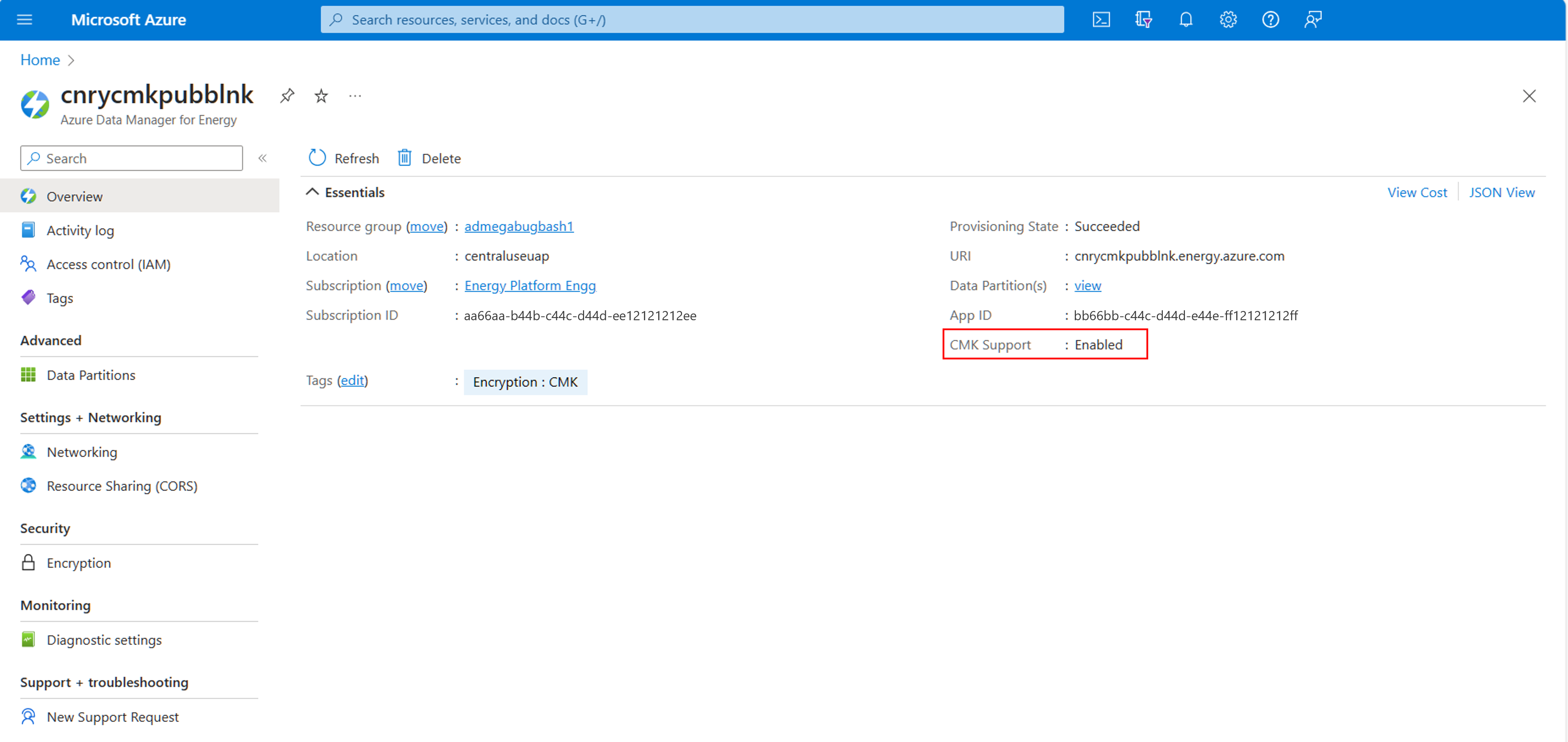
An Azure Data Manager for Energy instance is created with customer-managed keys.
Once CMK is enabled you will see its status on the Overview screen.
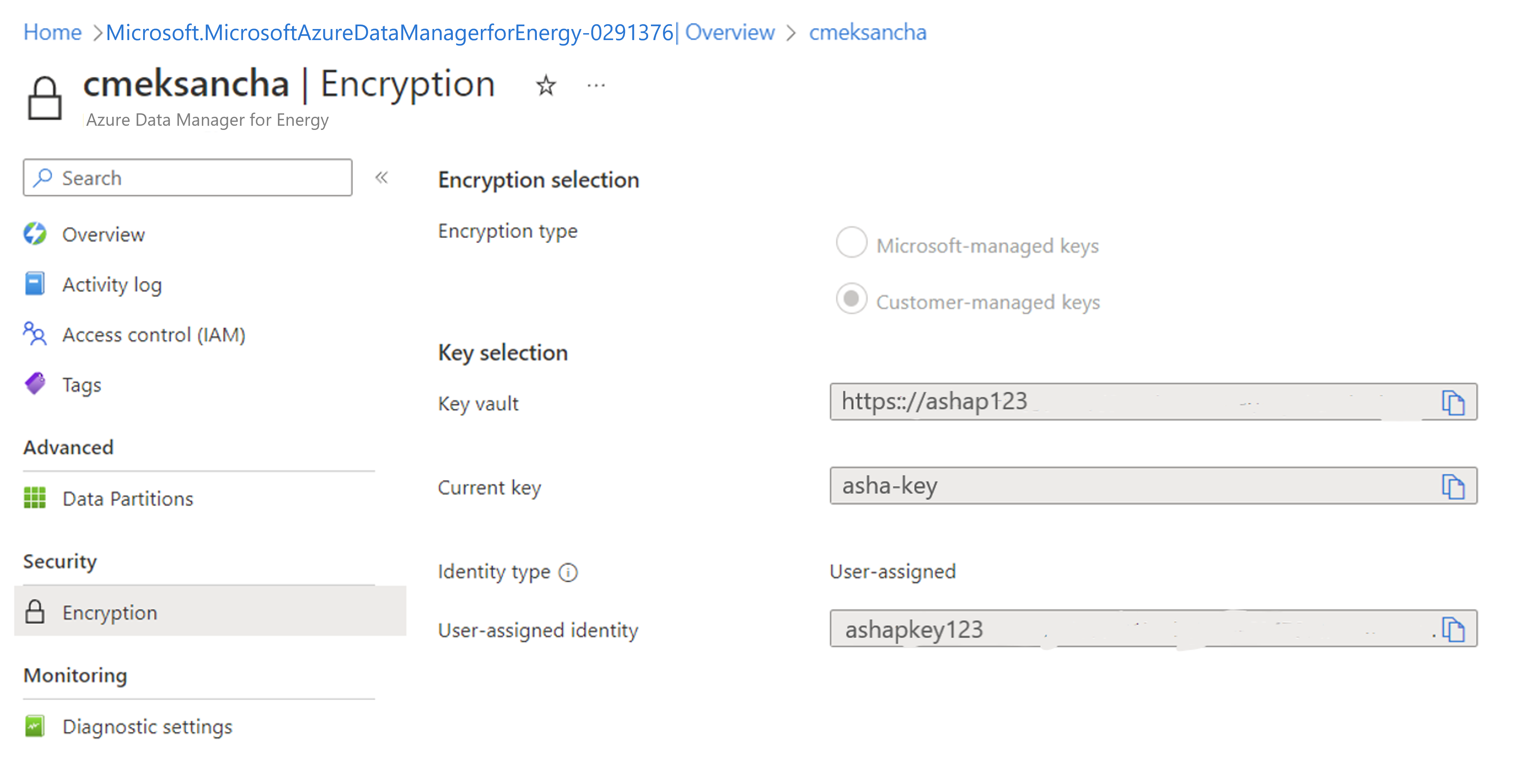
You can navigate to Encryption and see that CMK enabled with user managed identity.
Next steps
To learn more about Private Links.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for